Initiative on Security Issues of the IPv6 Protocol
Initiative on Security Issues of the IPv6 ProtocolTo all those concerned
09-25-2013 (Created)
04-28-2014 (Updated)
Support for IPv6 is spreading at an accelerated rate in network devices and Internet connection service menus. Today, an environment in which IPv6 can be used is becoming increasingly commonplace. From the perspective of network administration including security, IPv6 comes with features that need to be handled with an approach that differs from IPv4.
Under these circumstances, JPCERT/CC is investigating IPv6, while compiling matters that require attention upon implementing IPv6-enabled functionality on network devices and when using such devices in order to help educating relevant parties on such matters as outlined below.
1) Investigation of security issues related to IPv6 specifications
In fiscal 2012, we studied RFCs, Internet-Drafts and other resources to investigate the security issues that exist with respect to IPv6, including the methods of attack and deliberated on countermeasures that can be taken. This investigation was carried out with the participation of experts in the field. The possibility of attack, countermeasures, and other related matters were discussed in regard to "problems attributable to IPv6 specifications" and "service protocols used with IPv6, such as multicast and DNS." The results of this investigation have been compiled into the "Investigation Report on Security Issues Related to the IPv6 Protocol." An abridged version of this report that omits portions relating to problems with no definite countermeasures is available on the JPCERT/CC website.
2) Impact study of individual products with respect to security issues in implementing IPv6
In fiscal 2013, we investigated routers, L3 switches and some other IPv6-enabled devices by individual product to assess the status of their IPv6 readiness based on the "Investigation Report on Security Issues Related to the IPv6 Protocol." This investigation is conducted by providing vendors developing network devices with information on IPv6 security issues, as well as information on how to verify each issue and how to use verification support tools, then having vendors who agree with the aims of this investigation submit the verification results corresponding to the provided information. In the investigation for fiscal 2013, information is handled as illustrated in Figure 1.
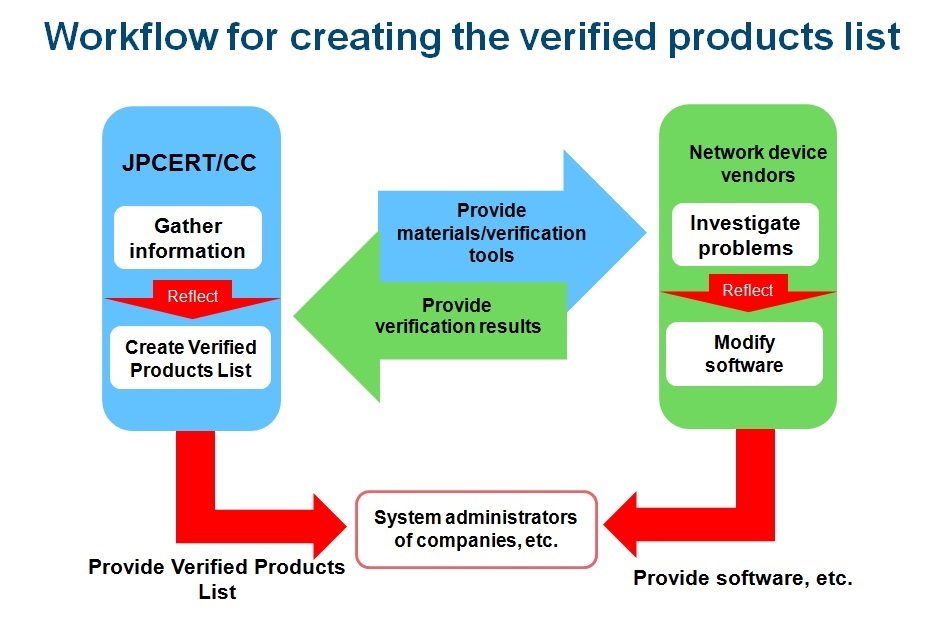
At JPCERT/CC, we compiled the verification results submitted by network device vendors and created the "IPv6 Security Test Verified Products List."
Further, we created the "IPv6 Security Test Verification Items Manual" for each verification item.
The IPv6 Security Test Verified Products List and the Verification Items Manual is available from here.
This product list will be updated as needed based on information provided by network device vendors.
See below for procedures for getting products listed on the Verified Products List.
■ Applications now open for IPv6-enabled product security test (11/21/2013)
We have determined the verification items and methods for the "IPv6 Security Test" and are now ready to accept applications from network device vendors wishing to participate in the test.
How to conduct the test and be included on the "IPv6 Security Test Verified Products List"
If you are interested in participating in the "IPv6 Security Test," please contact us at ipv6test-sec@jpcert.or.jp using the form below. We will send you "Test Item List" and "IPv6 Security Test Application Form."
Click here for the application form: for IE and other browsers
After reviewing the "Test Item List," please fill in the necessary items on the "IPv6 Security Application Form" and send it to us if you wish to conduct the test. We will then provide you with materials including a test manual and test tools. (You will be required to consent to our rules on the handling of materials and tools.)
When the test is completed, write down the test results on the "Information Provision Form" that we will send with the test materials, then submit the form, provided that you consent to our including the results on the "IPv6 Security Test Verified Products List." We will compile the submitted information into a list and publish it on our website.
■ Publication of the IPv6 Security Test Verified Products ListAt JPCERT/CC, we examined known issues identified in RFCs and Internet-Drafts published by IETF, and selected 15 issues related to routers, L3 switches and other IPv6-enabled network devices that companies use to connect to the Internet on the basis of susceptibility to Internet-based attacks. We then created the "IPv6 Security Test Manual" describing the test items and procedures. We had IPv6-enabled device vendors verify their products in accordance with this manual.
Here we publish the "IPv6 Security Test Verified Products List (2013)," which compiles the verification results submitted by IPv6-enabled device vendors and the "IPv6 Security Test Manual (For General Release)," which outlines the verification procedure.
The "IPv6 Security Test Verified Products List (2013)" and "IPv6 Security Test Manual (For General Release)" are intended for use as reference materials by the system administrators of companies and other organizations considering the purchase of IPv6-enabled devices.
| Date | title | |
|---|---|---|
| 2015-04-08 | IPv6 Security Test Manual (For General Release) 2013 | 317KB(PGP) |
| 2015-04-09 | IPv6 Security Test Verified Products List (2015/04/09) | 199KB(PGP) |

